How do you know whether the PMO is contacting you, or whether it is a charlatan? What signs should you look out for to guard yourself against giving away your sensitive data to scammers? Read on as we go over exactly how you connect to our systems and how we contact you.
Everything else should be suspect.
How you connect
Your gateway to everything is EU Login. You connect by entering your private email address and password. You need to use two-factor authentication to login. This means there is a second verification by the system after you introduce your email address and password.
Please watch the below video for more information on the available authentication methods:
By default, EU Login will not send you e-mails to request you to reset your password. When your password expires, you will simply be asked to set a new password while logging in.
However, you will receive e-mails – sometimes with links – from EU Login only if you perform one of the below actions:
1. You go to “My Account” when logged in and select “Change Password.”
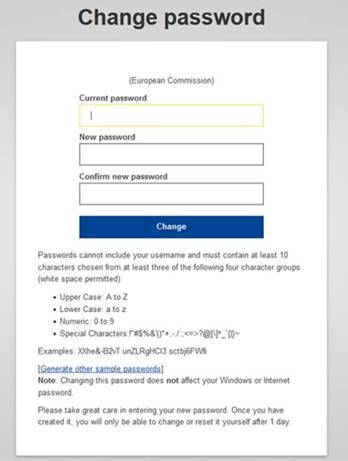
Then, an email is sent to your inbox confirming you have initiated the password reset yourself:

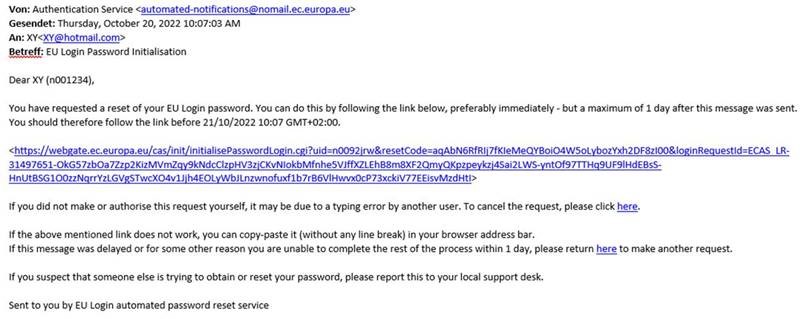
2. If you have forgotten your password, and have access to the email registered to your EU Login account, and you click on “Lost your password,” the following screen will appear:

At this point, an email will be sent to your registered email address and you must click on the link provided in the email, in order to reset your password:
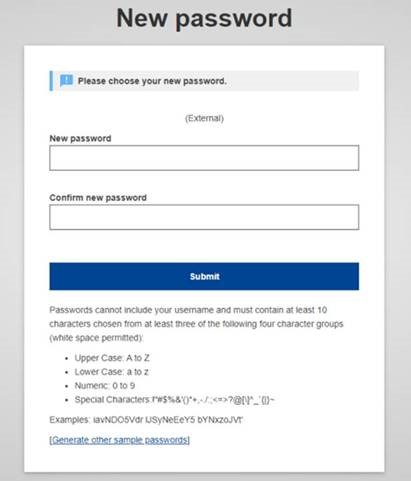
After clicking on the link, you will be redirected to this EU Login screen, whereupon you can choose a new password that matches the criteria mentioned:
After changing your password successfully, the following screen appears:

Note that if you have forgotten your password and insert the incorrect password, the following screen will appear and you will simply have to follow the steps laid out in (2) just the same:

Be careful: if you have not initiated this procedure in order to request to change your password, or to recover a forgotten password, any unsolicited emails prompting you to update your password are suspicious!
Via EU Login, you connect to My Remote, which is a safe space where you can access your platforms:

Note: you will not have access to “MyIntraComm – End of Contract” unless you are unemployed (as opposed to being a pensioner).
Fake EU Login Authentication requests scam
EU Login is also a target for scammers and, as such, its security is being continuously improved to protect your account.

If you use the app for multifactor authentication, please note that from 31 October the way you receive authentication requests on your mobile device has changed.
Push notifications will no longer pop up on your device when authenticating your login to EU services by PIN code or biometrics (fingerprint, etc.). From now on, these requests appear inside the app, making it even safer – see how it works.
If you get an ‘authentication’ pop-up from your EU Login Mobile app, it is most probably fake – do not validate it. Instead, please change your password immediately and contact the EC IT Helpdesk by calling +32 2 29 77 777.
How we contact you
Email communications
PMO colleagues handling your files may contact you by email for a number of reasons, such as to check your address if the post was returned, to request complementary documents, to confirm details surrounding your data, or to correct a mistake.
However, when it is one of us, the sender email address will always end with @ec.europa.eu.
Phone communications
Exceptionally, PMO colleagues may contact you by telephone to resolve a number of issues, such as to explain the reasoning behind a debt, to talk about a direct reimbursement, among others. However, we will never call you to clarify your bank account details or to ask for your bankcard number or PIN code.

When it is one of us calling from Brussels, the phone number will always begin with +32 2 29.
If the JSIS Ispra Helpdesk is calling you, the call will come from the following number: +39 0332 78 3030.
If a JSIS Luxembourg colleague is calling you, the phone number will always begin with +352 4301.
All JSIS calls will refer to your recent JSIS claims or opened Staff Contact tickets.
Three tips to recognise email scam attempts
1. The first thing to look for is the sender’s email address – if it does not end in @ec.europa.eu then you should be careful!
2. If the email is unsolicited, and it contains an attachment, watch out! Scammers often attach malware (viruses) together with their communications.

3. Be wary of any email that seeks to create a sense of urgency. The scam artist is seeking to get you to act irrationally through fear, overlooking inconsistencies in their request.
Three tips to recognise phone scam attempts
1. Phone scammers will always try to convince you that they are calling about something important or urgent.
2. Scammers either promise (“We will pay you more money”) or threaten (“If you do not confirm your bank details, we cannot make your payment”).
3. Scammers insist that you act immediately, taking advantage of your emotions or anxieties.
Act rationally and you will keep your money and identity. Ask follow-up questions, ask for time to think and a number to call back – or just hang up!
When we call you, we will never pressure you to make an important decision and act immediately.
Paper documents and fraud
Did you know that paper documents can increase your vulnerability to fraud?
For cybersecurity professionals, it’s long been clear that discarded paper documents are an invaluable source of personal information for fraudsters, and help them appear more convincing.
Maybe the polite lady on the phone isn’t from the PMO at all, but found your pensioner number on the pension slip you recently threw away. Perhaps she learned that you were covered by the JSIS from the old document pile you threw out some time ago.
The less paper files you use, the harder you will make it for scammers to obtain such clues about you. Your rights and pension slips are visible on SYSPER Post Activity. You can track all your medical claims using JSIS Online – or, even better, with PMO Mobile. Your old account sheets are also securely stored there for your reference.
Do you want to find out more?
Read on if you wish to learn more about the different types of cybercriminal activity: